We are committed to keeping any and all personal information collected of those individuals that visit our website and make use of our online facilities and services accurate, confidential, secure and private. Our privacy policy has been designed and created to ensure those affiliated with Upstream+ of our commitment and realization of our obligation not only to meet but to exceed most existing privacy standards.
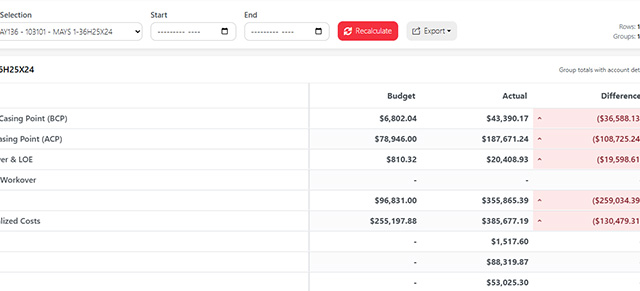
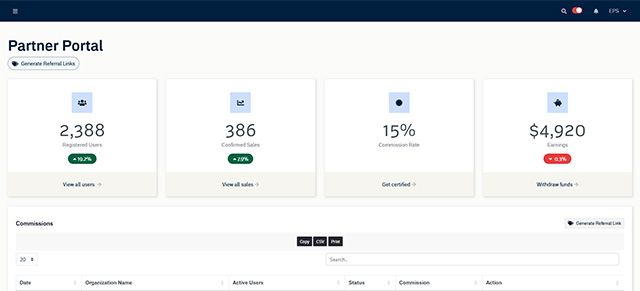
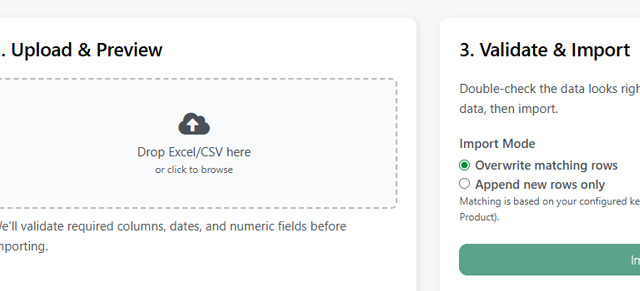
Who we are: Performance Flow Metrics (PFM) operates Upstream Reporting, a SaaS platform for oil & gas lease operating statements and related accounting/reporting.
Data ownership: Customers retain ownership of their accounting data and reports. PFM processes Customer Data only to deliver the Service.
High-level protections: Industry-standard cloud hosting, TLS for data in transit, AES encryption of data at rest, multi-factor authentication (MFA), role-based access control (RBAC), logging/monitoring, regular backups, and a tested incident response plan.
No unconditional code handover: Source code is never delivered on termination; code is only released under strictly defined sale/escrow or paid-assignment conditions.
Third-party subprocessors: We use vetted subprocessors (cloud host, payment processor, escrow agent). We have contractual DPAs and SCCs for international transfers.
Contact / evidence: To request security docs, reports, pen test summaries or the DPA, contact: support@performanceflowmetrics.com
Detailed security & privacy controls
1. Data protection (in transit & at rest)
- Encryption in transit: All network traffic to/from the Service uses TLS 1.2+ (TLS 1.3 where supported).
- Encryption at rest: Customer Data and backups are encrypted at rest using AES-256 or equivalent. Encryption keys are managed in a secure KMS.
- Key management: Keys are stored/managed via a secure, audited KMS; access is restricted to authorized DevOps/security personnel under dual-control policies.
2. Identity & access management
- Authentication: Support for enterprise SSO (Microsoft or Google) and Provider-managed accounts with strong password rules. MFA required for administrative accounts.
- Authorization: RBAC controls with least-privilege defaults; separation of duties for admin, dev and ops.
- Provisioning/deprovisioning: Integrations for SCIM/SSO-based provisioning; administrators can immediately revoke access.
- Session & token management: Short token lifetimes, refresh token rotation, and device/session visibility.
3. Network & infrastructure security
- Cloud infrastructure: Hosted on a major cloud provider (e.g., AWS). Use of private VPCs, network security groups, and strict egress/ingress controls.
- Segmentation: Customer environments logically partitioned; production, staging and dev environments are isolated.
- WAF & DDoS protection: Web application firewall and DDoS mitigation services in front of public endpoints.
4. Application security & development lifecycle
- Secure SDLC: Threat modeling, code reviews, static analysis (SAST) and dependency scanning incorporated into CI/CD pipelines.
- Penetration testing: Annual third-party penetration tests and scheduled internal/mock exercises; results and remediation tracked.
- Vulnerability management: Vulnerabilities triaged and remediated based on severity. Critical issues patched or mitigated within a defined SLA.
5. Logging, monitoring & detection
- Centralized logging: Application and infrastructure logs forwarded to an encrypted SIEM/monitoring system.
- Alerting & investigation: IDS/IPS signals, anomalous activity alerts, and 24/7/365 on-call procedures for critical incidents.
- Retention & audit trails: Audit logs of administrative and data access retained per policy (configurable).
6. Backup, continuity & disaster recovery
- Backups: Automated encrypted backups with geographically separate storage and periodic restoration testing.
- RTO / RPO: Defined Recovery Time Objectives and Recovery Point Objectives; periodic DR drills.
- Business continuity: Documented BCM plan and tested continuity procedures.
7. Data residency & international transfers
- Data residency options: Where required we can support region-specific hosting. Currently, all data is hosted in the continental United States.
- International transfers: Transfers protected by SCCs or other lawful transfer mechanisms; customers may request details or a copy of SCCs.
8. Subprocessors & third parties
- Subprocessor management: We maintain an approved list of subprocessors (cloud provider, payment processor, analytics, escrow provider). Subprocessors must sign DPAs and security obligations. Updated list available on request.
- Third-party assurance: We vet subprocessors for security posture and require SOC2/ISO or equivalent evidence where applicable.
More information can be found in our Data Security policy page.
Privacy & compliance highlights
- Data ownership & use: Customers own all Customer Data. We process Customer Data strictly to deliver the Service and per Customer’s instructions. Provider will not sell Customer Data.
- DPA & contractual protections: We offer a Data Processing Addendum consistent with GDPR/UK GDPR and CCPA/CPRA obligations, including subprocessors, breach notification timelines and audit rights.
- Data subject rights: For Customer Data, Customers are controllers and responsible for fulfilling data subject requests; we will assist as a processor. For provider-collected account metadata, we handle requests per policy.
- Breach notification: We will notify Customers of confirmed breaches affecting Customer Data without undue delay and in accordance with contractual timelines.
Operational & organizational controls
- Employee controls: Background checks for staff with production access; least-privilege access; annual security training.
- Change management: All changes go through change control, automated test suites and staged rollouts with rollback capability.
- Secrets management: Use secret stores for credentials, no plaintext secrets in source code or logs.
- Developer access: Access to production restricted and audited; emergency access requires logged approvals and post-mortem.
Incident response & disclosure
- Incident response program: Documented IR plan, playbooks, escalation and communication plans.
- Customer notification: If Customer Data is impacted, Provider will notify the Customer promptly and provide mitigation steps, root cause, impacted scope and remediation plan.
- Post-incident: Lessons learned, remediation tracking and periodic reporting on major incidents.